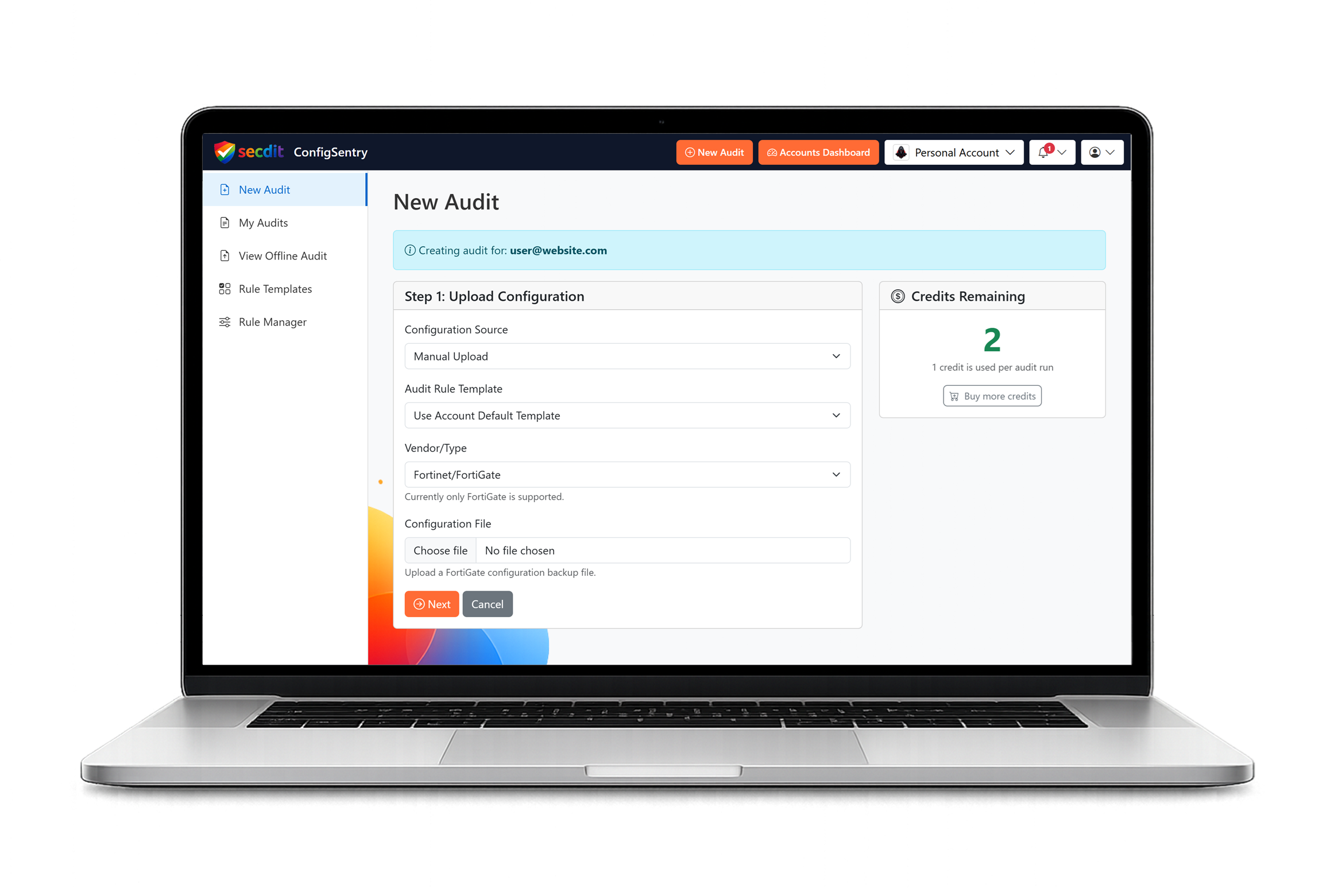
Provide the configuration
Start with an uploaded file or a collector-assisted connection path.
Product Overview
A focused FortiGate auditing platform built to turn configuration complexity into clear, actionable security understanding.
What ConfigSentry does
ConfigSentry is designed exclusively for Fortinet FortiGate firewalls and the review work that surrounds them.
It gives teams a clearer view of risky access, control gaps, drift, and security posture without forcing everything back into a slow manual review cycle.
Why firewall audits are hard
Rules grow, exceptions accumulate, and important access paths become harder to justify with confidence.
Even well-run environments drift away from the original design, which makes one-off point checks less useful unless the wider configuration context is preserved.
How ConfigSentry helps
The platform is built to highlight the issues that deserve attention first, with enough explanation to support remediation and review conversations.
That means less time sifting through noise and more time working from findings that reflect real configuration meaning.
Built for FortiGate-focused auditing
Unlike basic rule checkers, ConfigSentry evaluates the wider FortiGate configuration rather than a small subset of policy objects.
That broader view helps teams catch weaknesses that would otherwise sit outside a rule-only review.
From upload to actionable findings
The workflow stays simple, but the analysis keeps the context needed for a more trustworthy review.
Start with an uploaded file or a collector-assisted connection path.
Parse the FortiGate configuration into a structure that can be analysed consistently.
Run focused review logic against rules, objects, admin controls, and wider posture signals.
Review shareable output with clearer severity, context, and remediation direction.
Standards alignment and operating model
ConfigSentry can support point-in-time review, change validation, or a longer-term monitoring model depending on how your team works.
It also helps connect technical findings with recognised guidance and internal expectations without losing the practical risk context.
Explore further
Continue with how the workflow works, review example findings, or start with the free account and use real data.